Breaking News
Main Menu
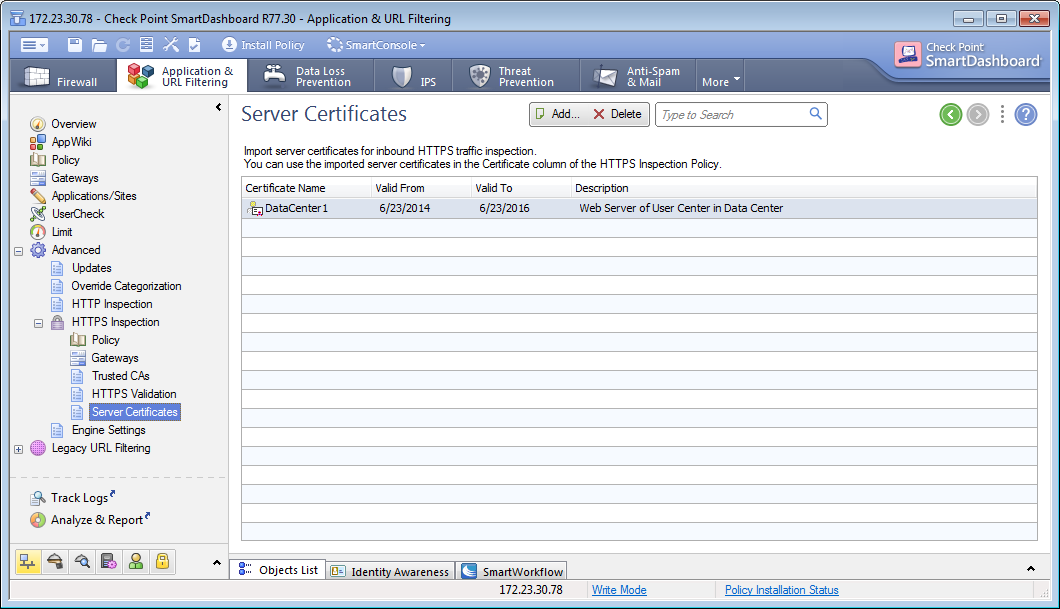
Checkpoint Smartdashboard Connection
суббота 02 февраля admin 55
Software Subscription Downloads allows registered access to product updates designed to keep your software as current as possible through the latest product enhancements and capabilities.
Configuration File Your integration team can provide you with a configuration file with the values you need in order to configure each tunnel and the IKE and IPsec settings for your VPN device. The configuration file includes instructions on how to use the Gaia web portal and Check Point SmartDashboard to configure your device. The same steps are provided in the next section. The following is an extract of an example configuration file. The file contains two sections: IPSec Tunnel #1 and IPSec Tunnel #2.
You must use the values provided in each section to configure each tunnel. Amazon Web Services! Virtual Private Cloud! AWS uses unique identifiers to manipulate the configuration of!
A VPN connection. Each VPN connection is assigned an identifier and is! Associated with two other identifiers, namely the! Customer gateway identifier and virtual private gateway identifier.!! Your VPN connection ID: vpn-12345678! Your virtual private gateway ID: vgw-12345678! Your customer gateway ID: cgw-12345678!!!
This configuration consists of two tunnels. Both tunnels must be! Configured on your customer gateway.!! IPSec Tunnel #1!
#1: Tunnel Interface Configuration.! IPSec Tunnel #2! #1: Tunnel Interface Configuration. Configuring the Check Point Device The following procedures demonstrate how to configure the VPN tunnels, network objects, and security for your VPN connection. You must replace the example values in the procedures with the values that are provided in the configuration file. Topics • • • • • • Step 1: Configure the Tunnel Interfaces The first step to create the VPN tunnels and provide the private (inside) IP addresses of the customer gateway and virtual private gateway for each tunnel.
For the first tunnel, use the information provided under the IPSec Tunnel #1 section of the configuration file. For the second tunnel, use the values provided in the IPSec Tunnel #2 section of the configuration file. To configure the tunnel interface • Connect to your security gateway over SSH. If you're using the non-default shell, change to clish by running the following command: clish • Set the customer gateway ASN (the ASN that was provided when the customer gateway was created in AWS) by running the following command. Save config Step 2: Configure BGP In this step, you create a BGP policy that allows the import of routes that are advertised by AWS. Then, configure your customer gateway to advertise its local routes to AWS.
To create a BGP policy • In the Gaia WebUI, choose Advanced Routing, Inbound Route Filters. Download jogo yugioh forbidden memories para pc. Choose Add, and select Add BGP Policy (Based on AS).
• For Add BGP Policy, select a value between 512 and 1024 in the first field, and enter the virtual private gateway ASN in the second field; for example, 7224. • Choose Save. The following steps are for distributing local interface routes. You can also redistribute routes from different sources; for example, static routes, or routes obtained through dynamic routing protocols. For more information, go to the.

Savita bhabhi hindi episode 36 free download. To advertise local routes • In the Gaia WebUI, choose Advanced Routing, Routing Redistribution. Choose Add Redistribution From and select Interface.
• For To Protocol, select the virtual private gateway ASN; for example, 7224. • For Interface, select an internal interface. Step 3: Create Network Objects In this step, you create a network object for each VPN tunnel, specifying the public (outside) IP addresses for the virtual private gateway.